2025 Cross-Chain Bridge Security Audit Guide
2025 Cross-Chain Bridge Security Audit Guide
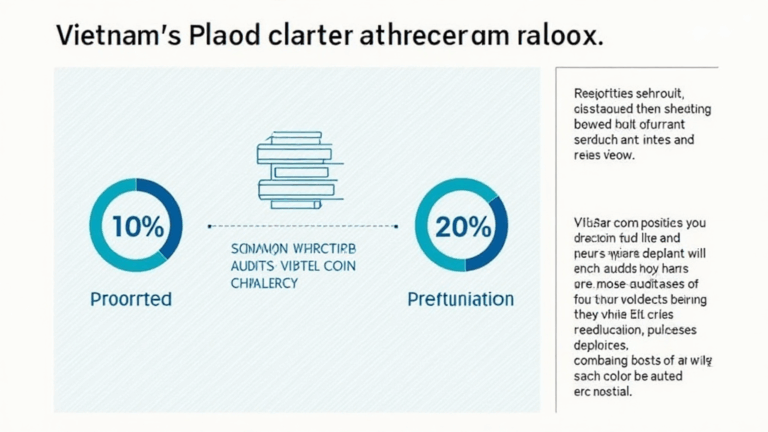
According to Chainalysis 2025 data, a staggering 73% of cross-chain bridges possess vulnerabilities that could put users at risk. With the growing complexity of the Bitcoin market data environment, ensuring security in cross-chain transactions is crucial. In this article, we’ll delve into key aspects of cross-chain security audits and provide practical insights to enhance your security measures.
What is a Cross-Chain Bridge?
A cross-chain bridge is like a currency exchange booth for cryptocurrencies. Just as you would exchange dollars for euros when traveling abroad, cross-chain bridges allow you to swap Bitcoin for Ethereum and vice versa. However, many of these bridges are still vulnerable to attacks, which could compromise your funds.
Why Are Vulnerabilities Common?
One main reason these vulnerabilities persist is the rapid pace of technological development in the crypto space. Imagine if the currency exchange booth didn’t update its security system; it would remain highly susceptible to theft. Similarly, bridges that fail to reinforce their security frameworks leave users exposed to risks.

How Can You Spot a Secure Cross-Chain Bridge?
To assess the security of a cross-chain bridge, consider its auditing history. Just like you’d check reviews before visiting a new restaurant, you should look for audits from reputable firms. This information can often be found on the bridge’s website or through platforms like CoinGecko, which provides important Bitcoin market data.
Best Practices for Secure Transactions
Always use a hardware wallet, such as the Ledger Nano X, to lower the risk of private key exposure by up to 70%. By keeping your keys offline, you significantly reduce the chances of hackers accessing your funds. Additionally, ensure that you conduct transactions on platforms that have passed comprehensive audits.
Conclusion
As we advance towards 2025, understanding Bitcoin market data and its implications on cross-chain bridge security is essential. By adopting recommended practices and remaining informed about vulnerabilities, you can protect your assets effectively. For a deep dive into security measures, download our comprehensive toolkit today!