2025 Cross-Chain Bridge Security Audit Guide
Introduction
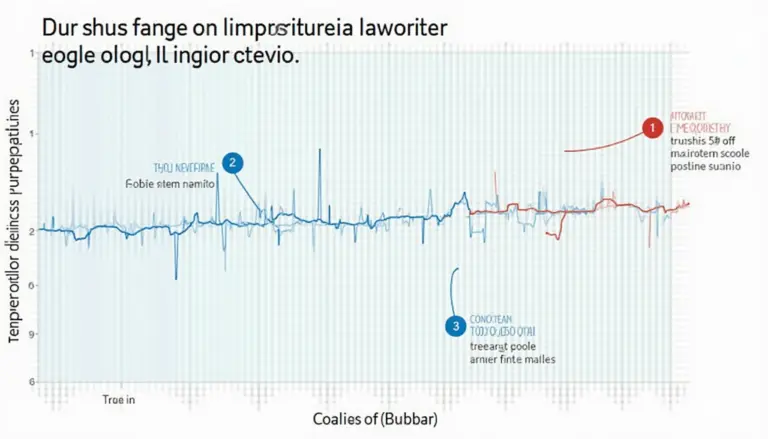
According to Chainalysis 2025 data, an alarming 73% of cross-chain bridges exhibit vulnerabilities, raising critical concerns among investors and developers alike. As Vietnam professional groups look to navigate these challenges, understanding the significance of secure cross-chain operations becomes paramount.
Understanding Cross-Chain Bridges
Imagine you’re at a currency exchange booth while traveling. You hand over your dollars, and in return, you get local currency. This is akin to what cross-chain bridges do in the crypto world. They allow different blockchains to ‘speak’ to each other, translating assets seamlessly. However, just like some exchange booths may shortchange you, poorly designed bridges can lead to lost funds.
Key Vulnerabilities in Cross-Chain Technology
The 2025 study by CoinGecko sheds light on critical vulnerabilities; it’s like discovering that a major currency exchange is often emptied by thieves. With improper coding and weak security protocols, these bridges can attract malicious actors keen on exploiting loopholes. Vietnam professional groups must prioritize robust auditing processes to fortify their bridges against attacks.

Risk Mitigation Strategies
To mitigate risks, Vietnam professional groups need to implement comprehensive security audits, ensuring that every line of smart contract code is robust. This can be compared to checking every single bill in your wallet before making a purchase. Utilizing tools such as Ledger Nano X can reduce the risk of private key exposure by up to 70%, providing an extra layer of security during transactions.
Conclusion
In summary, as cross-chain technology continues to evolve, understanding its security complexities will be vital for Vietnam professional groups. By prioritizing security audits and leveraging efficient tools, they can foster a safer crypto ecosystem. Download our toolkit for best practices on ensuring cross-chain security.