2025 Cross-Chain Bridge Security Audit Guide
2025 Cross-Chain Bridge Security Audit Guide
According to 2025 data from Chainalysis, a staggering 73% of cross-chain bridges exhibit vulnerabilities that could jeopardize crypto assets. As the DeFi landscape continues to evolve, ensuring robust security is more crucial than ever. In this article, we will explore HIBT crypto security best practices to help secure your transactions and investments.
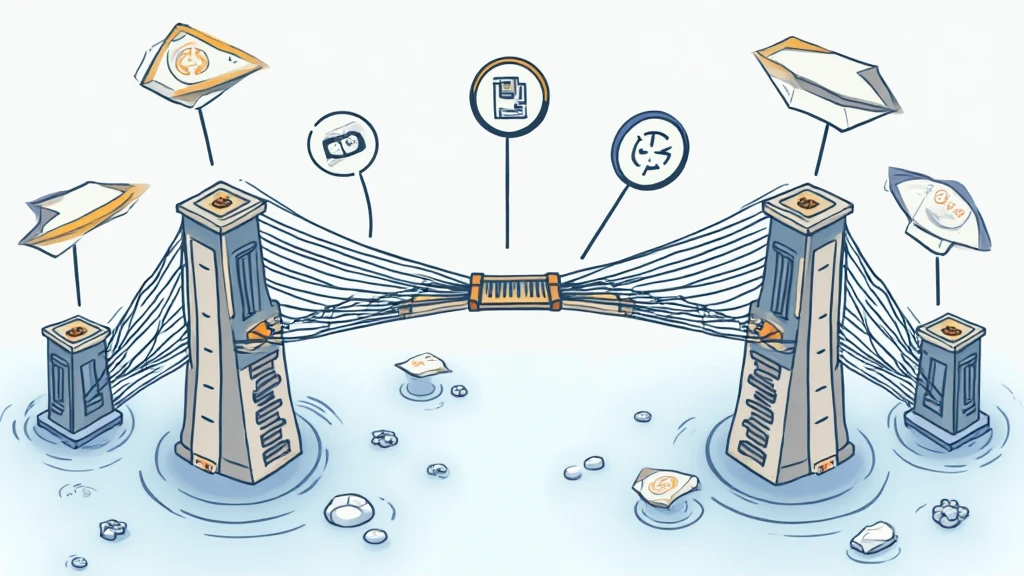
What are Cross-Chain Bridges?
Imagine you’re at a currency exchange booth at a busy market. Just as you exchange one currency for another, cross-chain bridges allow you to transfer assets across different blockchain networks. However, not all booths are equally secure. Many vulnerabilities exist that can be exploited by malicious actors.
Understanding Zero-Knowledge Proof Applications
Zero-knowledge proofs can be likened to a game of guessing. You can prove that you have a piece of information (like a secret) without revealing the information itself. This cryptographic technique is essential in enhancing privacy and security in transactions, especially within cross-chain interactions, making it a best practice for HIBT.
Best Practices for Monitoring Cross-Chain Transactions
Much like a watchful shopkeeper overseeing transactions, you need to monitor your asset transfers continuously. Implementing automated alerts for unusual activities can act as your first line of defense against potential hacks and losses. Using platforms like CoinGecko can provide real-time data and alerts for suspicious transactions.
Tools for Enhancing Security: Ledger Nano X
Think of the Ledger Nano X as a safe in your home. Instead of keeping valuables out in the open, this hardware wallet securely stores your private keys and protects you from up to 70% of the risks associated with key exposure. When using cross-chain bridges, this added layer of security can significantly reduce potential losses.
Conclusion
As we approach 2025, staying informed on HIBT crypto security best practices is crucial for anyone participating in the crypto space. By understanding cross-chain bridges, leveraging zero-knowledge proofs, actively monitoring transactions, and using secure tools like Ledger Nano X, you can better protect your assets. We invite readers to download our comprehensive security toolkit at hibt.com to enhance their crypto security measures.
Disclaimer
This article does not constitute investment advice. Please consult your local regulatory authority prior to taking action.